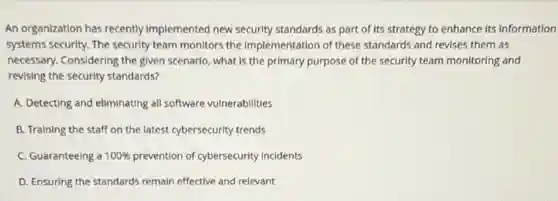
An organization has recently Implemented new security standards as part of Its strategy to enhance Its information systems security. The security team monitors the Implementation of these standards and revises them as necessary. Considering the given scenario, what is the primary purpose of the security team monitorIng and revising the security standards? A. Detecting and eliminating all software vulnerabilities B. Training the staff on the latest cybersecurity trends C. Guaranteeing a 100% prevention of cybersecurity incidents D. Ensuring the standards remain effective and relevant
Solution4.6(152 votes)
Answer
Explanation
Similar Questions
Fill in the blank with the correct words. WordPress displays a list of $\square $ that match your $\square $
What is the intersection of a row and column in a table called? placeholder cell data points axis
Once a variable gets a value, you cannot change its value. True C False
True or False? The first step in active reconnaissance is the gathering of information about software in use by the target. True False
Of the options below, what is the most important consideration when designing a high-availability network? (pick two) A. Ease of recovery B. Ability to patch C. Attack surface D. Physical isolation E. Extensible authentication F. Responsiveness
¿Qué escenario o situación impediria que un usuario actualice el sistema operativo en un dispositivo Android? No se instalaron los parches correctos. Los derechos de autor del software no se obtuvieron antes de la instalación. El hardware no cumple con las especificaciones. No se obtuvo el permiso del fabricante.
You need to deploy a new web application firewall, and you're comparing different solutions according to what kinds of rules they can process, how many requests they can handle per second how much they affect website response time , and how much training it takes for administrators to design and apply rules. What kind of metrics are not currently included in your comparison? Choose all that apply. Usability Latency Capability Maintainability Scalability
There are three network levels. True False
¿Cuáles el Objetivo Personal SMART S1 que usted se propuso? Escribe tu respuesta aqui
When you start to $type=AV,$ what feature displays a list of functions and defined names? A. Function ScreenTip B. Insert Function dialog box C. Function Arguments dialog box D. Formula AutoComplete









